Share
DUBAI, United Arab Emirates — Dozens of journalists at Al-Jazeera, the Qatari state-owned media company, have been targeted by advanced spyware in an attack likely linked to the governments of Saudi Arabia and the United Arab Emirates, a cybersecurity watchdog said Sunday.
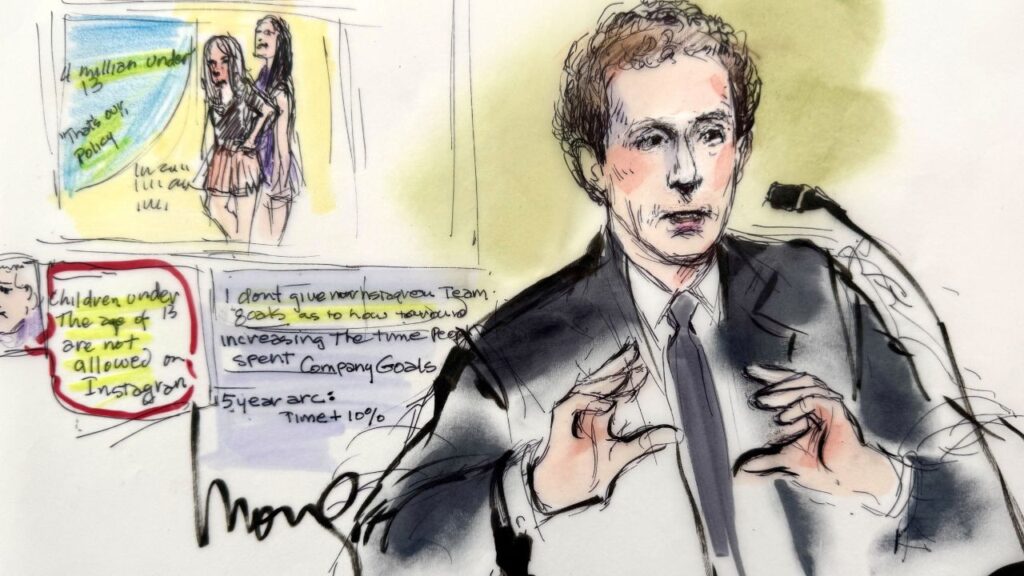
Citizen Lab at the University of Toronto said it traced malware that infected the personal phones of 36 journalists, producers, anchors and executives at Al-Jazeera back to the Israel-based NSO Group, which has been widely condemned for selling spyware to repressive governments.
Most unnerving to the investigators was that iMessages were infecting targeted cellphones without the users taking any action — what’s known as a zero-click vulnerability. Through push notifications alone, the malware instructed the phones to upload their content to servers linked to the NSO Group, Citizen Lab said, turning journalists’ iPhones into powerful surveillance tools without even luring users to click on suspicious links or threatening texts.
The coordinated attacks on Qatari-funded Al-Jazeera, which Citizen Lab described as the largest concentration of phone hacks targeting a single organization, occurred in July, just weeks before the Trump administration announced the normalization of ties between Israel and the UAE, the archival to Qatar. The breakthrough deal took public what had been a long-secret alliance. Analysts say normalization likely will lead to stronger cooperation in digital surveillance between Israel and Persian Gulf sheikhdoms.
Apple said it was aware of the Citizen Lab report and said the latest version of its mobile operating system, iOS 14, “delivered new protections against these kinds of attacks.” It sought to reassure users that NSO doesn’t target the average iPhone owner, but rather sells its software to foreign governments to target a limited group. Apple said it has not been able to independently verify Citizen Lab’s analysis.
Citizen Lab, which has been tracking NSO spyware for four years, tied the attacks “with medium confidence” to the Emirati and Saudi governments, based on their past targeting of dissidents at home and abroad with the same spyware. The two countries are embroiled in a bitter geopolitical dispute with Qatar in which hacking and cyber surveillance have increasingly become favored tools.
The Spyware Was Implicated in the Gruesome Killing of Saudi Journalist Jamal Khashoggi
In 2017, the two Gulf nations and their allies imposed a blockade on Qatar over its alleged support for extremist groups, a charge Doha denies. The UAE and Saudi Arabia served the tiny country with a list of demands, among them shutting down its influential Arabic-language TV network, which the UAE and Saudi Arabia see as promoting a political agenda at odds with their own. The feud continues to fester, although officials recently have indicated a resolution may be within reach.
Emirati and Saudi authorities did not respond to requests for comment.
The NSO Group cast doubt on Citizen Lab’s accusations in a statement but said it was “unable to comment on a report that we have not yet seen.” The firm said it provides technology for the sole purpose of enabling “governmental law enforcement agencies to tackle serious organized crime and counterterrorism.” Nevertheless, it added, “when we receive credible evidence of misuse … we take all necessary steps in accordance with our product misuse investigation procedure in order to review the allegations.” NSO does not identify its customers.
Prior to Sunday’s report, NSO’s spyware has repeatedly been found deployed to hack journalists, lawyers, human rights defenders and dissidents. Most notably, the spyware was implicated in the gruesome killing of Saudi journalist Jamal Khashoggi, who was dismembered in the Saudi consulate in Istanbul in 2018 and whose body has never been found. Several alleged targets of the spyware, including a close friend of Khashoggi and several Mexican civil society figures, sued NSO in an Israeli court over the hacking.
The NSO Group’s surveillance software, known as Pegasus, is designed to bypass detection and mask its activity. The malware infiltrates phones to vacuum up personal and location data and surreptitiously control the smartphone’s microphones and cameras, allowing hackers to spy on reporters’ face-to-face meetings with sources.
“It’s not only very scary, but it’s the holy grail of phone hacking,” said Bill Marczak, a senior researcher at Citizen Lab. “You can be using your phone normally, completely unaware that someone else is looking at everything you’re doing.”
‘It’s a Horrible Feeling to Be So Insecure’
The Citizen Lab researchers connected the hacks to previously identified Pegasus operators in attacks attributed to Saudi Arabia and the UAE over the last four years.
Rania Dridi, a newscaster at the London-based satellite channel Al Araby, never noticed anything amiss. Although she said she’s accustomed to Emirati and Saudi criticism over her reporting on human rights and the UAE’s role in wars in Libya and Yemen, she was shocked to learn her phone had been infected with invasive spyware on several occasions starting October 2019.
“It’s a horrible feeling to be so insecure, to know my private life wasn’t private this whole time,” she said.
The zero-click vulnerability is increasingly being used to hack cellphones without a trace, said Marczak. Last year, WhatsApp and its parent company Facebook filed an unprecedented lawsuit against the NSO Group, accusing the Israeli firm of targeting some 1,400 users of its encrypted messaging service with highly sophisticated spyware through missed calls. Earlier this month, an Al-Jazeera anchor filed another lawsuit in the U.S., alleging that the NSO Group hacked her phone through WhatsApp over her reporting on Saudi Arabia’s powerful Crown Prince Mohammed bin Salman.
With the UAE and Bahrain normalizing ties with Israel, the use of Israeli spyware in the region may accelerate, Marczak added, encompassing a “much wider range of government agencies and customers across the Gulf.”
The Al-Jazeera attack represents the tip of the iceberg, said Yaniv Balmas, head of cyber research at Check Point, an Israeli security company.
“These hacks are not supposed to be public,” he said. “We should assume they’re happening all the time, everywhere.”
RELATED TOPICS:
Categories

What You Need to Know About Avalanche Safety in the Backcountry